Here are some Safety and Security Guidelines for Combating Virus and Malware. The following are steps and precautions that any pc user can take to minimize or eliminate the chances of getting hit by a virus or malware.
Safety and Security Guidelines for Combating Virus and Malware:
1. Installing an anti-virus software
Installing an anti-virus software is an essential step in combating against viruses and malware.
Anti-virus software works by scanning your computer for any malicious programs or files, and helps to prevent viruses and malware from infecting your computer.
It’s important to choose a reputable anti-virus software that is known for its effectiveness and reliability. Some popular options include Norton, McAfee, Kaspersky, and Avast.

Some Popular antivirus Software Programs.
These programs offer features such as real-time scanning, automatic updates, and the ability to schedule scans.
Once you have installed your anti-virus software, make sure to keep it up-to-date with the latest virus definitions and security patches. This ensures that your computer is protected against the latest threats.
Regularly scanning your computer with your anti-virus software is also important to identify and remove any threats. You can choose to schedule regular scans, or run them manually as needed.
NOTE:
It’s important to note that anti-virus software is not foolproof and cannot guarantee complete protection against all threats.
Therefore, it’s important to follow other safety and security guidelines, such as keeping your operating system and software up-to-date, using strong passwords, and being cautious with email attachments and downloads.
Conclusion:
Installing and using reputable anti-virus software, keeping it up-to-date, and regularly scanning your computer are important steps in protecting your computer from viruses and malware.
But it’s important to remember that anti-virus software is just one part of a comprehensive security plan.
By following other safety and security guidelines, you can ensure that your computer and personal data are as protected as possible.
2. Use Strong Passwords:
Using strong and unique passwords for all your online accounts is crucial in keeping your personal information secure.
Weak passwords that are easily guessable, such as “123456” or “password”, can leave your accounts vulnerable to hacking and unauthorized access.
When creating a strong password, it’s important to use a combination of upper and lower case letters, numbers, and special characters.
Avoid using easily guessable information such as your name, date of birth, or phone number, as this information can be easily obtained by hackers.
It’s also important to use a unique password for each of your accounts, rather than using the same password for multiple accounts.
This is because if one account is compromised, all your other accounts with the same password will also be vulnerable.
Password Managers
Another useful strategy is to use a password manager, which is a tool that helps you generate, store, and manage strong and unique passwords for all your accounts.

Password managers are a secure way to store all your passwords, and can even automatically fill in your login information for you when you visit a website.
In addition to using strong passwords, it’s also important to enable two-factor authentication whenever possible.
Two-factor authentication adds an extra layer of security by requiring a second form of verification, such as a code sent to your phone, in addition to your password.
Overall, using strong and unique passwords, and enabling two-factor authentication, are essential steps in protecting your personal information and accounts from unauthorized access.
By following these guidelines, you can greatly reduce the risk of your accounts being compromised by hackers.
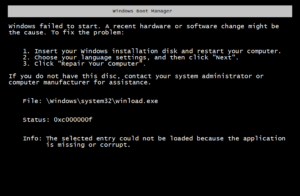
3. Update your Operating System and System Software
Keeping your operating system and software up-to-date is an important part of maintaining the security of your computer.
This is because updates often include security patches that fix known vulnerabilities and protect against potential threats.
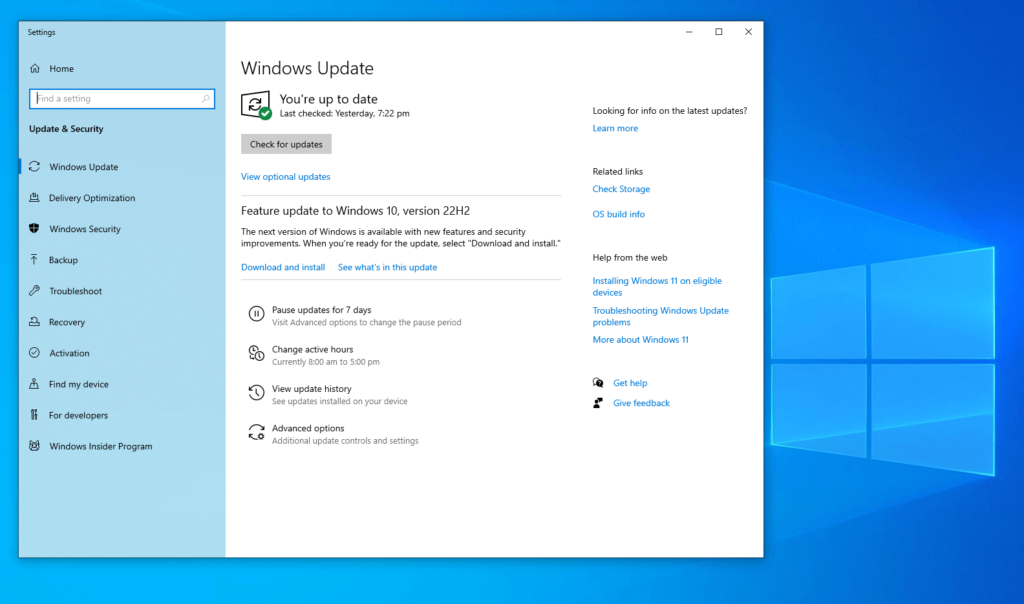
Failing to update your operating system and software can leave your computer vulnerable to cyber attacks and malware infections.
Most modern operating systems and software applications have built-in update mechanisms that will automatically notify you when updates are available.
It’s important to make sure that these mechanisms are enabled, so that you receive notifications when new updates become available.
When updates become available, it’s important to install them as soon as possible.
This is especially true for security updates, which often address critical vulnerabilities that could be exploited by hackers. Delaying updates can leave your computer vulnerable to these types of attacks.
In addition to installing updates as soon as they become available, it’s also important to make sure that you are running the latest version of your operating system and software.
Older versions may no longer receive security updates, and may contain known vulnerabilities that can be exploited by attackers.
Finally, it’s important to make sure that any third-party applications you have installed are also kept up-to-date. These include web browsers, plugins, and other software that may be vulnerable to attacks.
Many of these applications have automatic update mechanisms as well, so it’s important to enable these mechanisms and install updates as soon as they become available.
Conclusion:
Keeping your operating system and software up-to-date is an important step in maintaining the security of your computer.
By installing updates as soon as they become available, running the latest versions of your software, and keeping third-party applications up-to-date, you can reduce the risk of your computer being compromised by hackers and malware infections.
4. Use a Firewall
A firewall is an essential component of any computer security setup, as it acts as a barrier between your computer and the internet, helping to prevent unauthorized access and keeping your computer safe from cyber attacks.

A firewall works by monitoring the network traffic that passes between your computer and the internet, and filtering out any traffic that it deems suspicious or potentially dangerous.
This includes incoming traffic that may be trying to exploit vulnerabilities in your computer or install malware, as well as outgoing traffic that may be trying to send sensitive information to unauthorized recipients.
Most modern operating systems come with a built-in firewall, and it’s important to make sure that this firewall is enabled.
In addition to the built-in firewall, there are also third-party firewall programs available that provide additional features and functionality, such as more granular control over network traffic and advanced threat detection capabilities.
When using a firewall, it’s important to configure it properly to ensure that it provides maximum protection.

This includes configuring the firewall to block all incoming traffic except for traffic that is explicitly allowed, and configuring the firewall to monitor outgoing traffic to prevent sensitive information from being sent to unauthorized recipients.
It’s also important to keep your firewall up-to-date, as new threats and vulnerabilities are discovered all the time, and updates may be necessary to ensure that your firewall is providing the best possible protection.
Conclusion:
Using a firewall is an important step in maintaining the security of your computer.
By enabling your computer’s built-in firewall or installing a third-party firewall, configuring it properly, and keeping it up-to-date, you can greatly reduce the risk of your computer being compromised by hackers and malware.
5. Practice Caution with Email Attachments
Email is a common way for cybercriminals to distribute viruses and malware, so it’s important to be cautious with email attachments to prevent infection.
Phishing Emails
One of the best ways to protect yourself is to be wary of email attachments from unknown senders. These emails may be phishing emails or contain malware that can infect your computer.
It’s important to be particularly vigilant for emails with suspicious or unexpected attachments, as these are often used by cybercriminals to spread viruses and malware.

If you receive an email with an attachment that you’re not expecting, it’s best to err on the side of caution and not open it. Instead, try to verify the identity of the sender and the contents of the email before opening the attachment.
This can be done by contacting the sender directly or by checking the email address against a known source, such as a company’s official website.

Even if you do receive an attachment from a known sender, it’s important to scan it with your anti-virus software before opening it. This will help to ensure that any viruses or malware are detected and removed before they can cause damage to your computer.

Be Cautious with Email Attachments
In addition to being cautious with email attachments, it’s also important to be aware of other types of phishing emails and scams that may try to trick you into clicking on a malicious link or downloading malware.

These can include emails that appear to be from legitimate companies or organizations, but are actually fake and designed to steal your personal information or infect your computer.
Conclusion:
Being cautious with email attachments is an important step in maintaining the security of your computer.
By being wary of email attachments from unknown senders, not opening unexpected attachments, and scanning all attachments with anti-virus software, you can greatly reduce the risk of your computer being compromised by viruses and malware.
6. Be Weary of Suspicious Links
One of the most common ways that cybercriminals spread malware and viruses is through malicious links. These links can be found in emails, on websites, or in social media posts, and are designed to trick the user into clicking on them.
Once clicked, the user may be directed to a website that installs malware or be prompted to download an infected file.
To avoid falling victim to these types of attacks, it’s important to be vigilant and not click on any links that seem suspicious.
Here are some tips to help you avoid clicking on malicious links:
- Hover over the link: Before clicking on any link, hover your mouse over it to see the URL that it leads to. If the URL looks suspicious or doesn’t match the expected destination, don’t click on it.
- Only click on links from trusted sources: Only click on links from sources that you trust, such as known companies, organizations, or people that you have a relationship with.
- Be wary of shortened URLs: Shortened URLs, such as those used on Twitter, can be used to hide the true destination of a link. Be cautious when clicking on shortened URLs, and use a link preview tool to see where the link leads before clicking.
- Don’t open unsolicited emails: If you receive an unsolicited email with a link, don’t click on it. Instead, delete the email or mark it as spam.
- Keep your software up-to-date: Keeping your web browser and other software up-to-date can help protect against attacks that exploit known vulnerabilities.
Conclusion:
Clicking on suspicious links is a common way for cybercriminals to spread malware and viruses.
You can greatly reduce the risk of your computer being compromised by malicious links by being vigilant, hovering over links to check the URL, only clicking on links from trusted sources, being wary of shortened URLs, not opening unsolicited emails, and keeping your software up-to-date.
7. Two-Factor Authentication
Using two-factor authentication (2FA) is an effective way to enhance the security of your online accounts. With 2FA, you are required to provide a second authentication factor, in addition to your password, to gain access to your account.

This means that even if a cybercriminal obtains your password, they will not be able to access your account without the additional authentication factor.
Here are some benefits of using 2FA:
- Adds an extra layer of security: 2FA provides an extra layer of security, making it more difficult for cybercriminals to gain access to your accounts.
- Protects against password theft: Even if a cybercriminal steals your password, they will not be able to access your account without the additional authentication factor.
- Easy to use: 2FA is relatively easy to set up and use, and many online services and platforms offer 2FA as an option.
Multiple authentication methods: There are different types of 2FA methods available, such as receiving a verification code via text message, using an authentication app, or using a physical token.

To enable 2FA on your accounts, you will typically need to follow these steps:
- Log in to your account and go to the security or privacy settings.
- Look for the 2FA option and choose the method you want to use.
- Follow the instructions to set up 2FA for your account.
It’s important to note that while 2FA is an effective security measure, it is not foolproof. Cybercriminals may still be able to bypass 2FA using sophisticated attack techniques.
Therefore, it’s important to combine 2FA with other security measures, such as using strong passwords, keeping your software up-to-date, and being cautious with email attachments and suspicious links.
8. Regularly do Data Backup
Regularly backing up your data is a critical part of maintaining good cybersecurity practices.

By creating regular backups of your important files and documents, you can ensure that you can quickly and easily recover your data if your computer becomes infected with malware.
Here are some benefits of backing up your data regularly:
- Protects against data loss: Backing up your data regularly can help you to recover your information in case your computer becomes infected with malware or is otherwise compromised.
- Provides peace of mind: Knowing that your important files and documents are backed up in a safe and secure location can provide peace of mind and reduce stress in the event of a data loss incident.
- Facilitates recovery from hardware failure: Backing up your data can also help you to recover quickly in the event of hardware failure, such as a hard drive crash.
When backing up your data, it is important to ensure that your backups are stored in a secure location. This can include external hard drives or cloud-based backup services.
It is important to ensure that your backups are encrypted to protect your sensitive data in case of a security breach.
Here are some tips for backing up your data:
- Create a backup schedule: Schedule regular backups of your data so that you always have a recent backup available.
- Use multiple backup locations: Store your backups in multiple locations to ensure that you always have access to a backup, even if one location is compromised.
- Test your backups: Regularly test your backups to ensure that your data is being backed up correctly and that you can recover your data in case of a data loss incident.
By following these guidelines for backing up your data, you can ensure that your information is protected and that you can recover your data quickly and easily in case of a data loss incident.
9. Don’t Download Software from Untrusted Sources
Downloading software from untrusted sources is a common cause of malware infections.
Malicious actors often create fake or infected software that looks like legitimate software to trick users into downloading and installing it on their computers.
Once installed, this software can perform a wide range of malicious activities, such as stealing sensitive data, hijacking your computer, or spreading malware to other computers on your network.
To protect your computer from malware infections, it is essential to only download software from reputable sources.
Here are some guidelines to follow when downloading software:
- Use official sources: Download software from official websites or trusted app stores. These sources carefully vet software to ensure that it is safe and secure.
- Check the website reputation: Before downloading software from a website, check its reputation online. You can do this by searching for reviews or complaints about the website or using online tools that analyze the website’s security.
- Avoid pirated software: Downloading and installing pirated software can be dangerous, as it often contains malware. Pirated software is also illegal and can put you at risk of legal consequences.
- Be cautious with freeware: Freeware is software that is available for free, but it may contain advertising or other unwanted software. Only download freeware from reputable sources and carefully read the installation prompts to avoid installing any unwanted software.
- Use antivirus software: Use a reputable antivirus program that includes malware detection and removal. This software can help to identify and remove malware if it is installed on your computer.
By following these guidelines, you can help to protect your computer from malware infections that can be caused by downloading software from untrusted sources.
Remember that prevention is always better than cure, and taking these steps can help you to avoid the frustration and potential financial costs of a malware infection.
10. Educate Yourself:
Staying informed about the latest virus and malware threats and educating yourself on how to protect your computer is essential in preventing malware infections.

Malware attacks are constantly evolving, and attackers are always finding new ways to exploit vulnerabilities in computer systems.
Therefore, it’s crucial to stay up-to-date with the latest security news and educate yourself on how to protect your computer.
Here are some tips on how to educate yourself and stay informed:
- Attend online security courses: Many online courses offer in-depth training on computer security and malware threats. These courses provide a great opportunity to learn about best practices, new threats, and how to protect your computer.
- Read security blogs: Many security experts maintain blogs that cover the latest threats and provide tips on how to protect your computer.
- Follow security news sources: Keeping up-to-date with the latest security news is essential in understanding the latest threats and vulnerabilities. Follow trusted security news sources such as security magazines and online news portals to stay informed.
- Use online resources: There are many online resources available that provide information on malware threats and how to protect your computer. These include websites and forums that provide advice and support to users who have been infected with malware.
By educating yourself and staying informed about the latest threats, you can take proactive steps to protect your computer and avoid falling victim to malware infections.
Remember, prevention is always better than cure, and by staying informed, you can help protect yourself from the constantly evolving threat of malware.
Best Free Virus Protection Software
Final Thoughts
Conclusion: By following these Security Guidelines for Combating Virus and Malware, you can help to protect your computer from viruses and malware.
Remember to stay vigilant, keep your software up-to-date, and always be cautious with suspicious links, email attachments, and downloads.