Ransomware Data Recovery

I. Introduction to Ransomware Data Recovery
Ransomware is a type of malware that encrypts your data and demands a ransom payment in exchange for the decryption key.
Ransomware attacks can have devastating effects on businesses, causing data loss, financial loss, and reputational damage. In this guide, we’ll show you how to protect your business from ransomware attacks and how to recover your data if you get attacked.
II. How to protect your business from ransomware attacks
A. Employee training and education
One of the most effective ways to prevent ransomware attacks is to educate your employees about cybersecurity best practices.
This can include things like not clicking on suspicious links or downloading attachments from unknown senders, using strong passwords, and avoiding public Wi-Fi networks.
B. Regular software updates
Keeping your software up to date is essential for protecting against ransomware attacks. Cybercriminals often target vulnerabilities in outdated software, so make sure to install updates as soon as they become available.
C. Back up your data
Backing up your data is crucial for recovering from a ransomware attack. Make sure to regularly back up all your important data to a secure off-site location.
D. Implement firewalls and antivirus software
Firewalls and antivirus software can help protect your business from ransomware attacks by blocking suspicious traffic and detecting malware. Make sure to install and regularly update these tools.

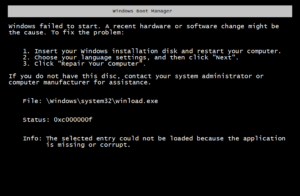
III. What to do if you get attacked
A. Disconnect from the internet
If you suspect that your business has been hit by a ransomware attack, the first thing you should do is disconnect from the internet. This can help prevent the malware from spreading to other devices.

B. Don’t pay the ransom
Paying the ransom may seem like the easiest way to get your data back, but it’s not recommended.
There’s no guarantee that the attackers will actually give you the decryption key, and paying the ransom can encourage them to target your business again in the future.
C. Report the attack
Reporting the attack to the appropriate authorities can help them track down the attackers and prevent future attacks.
Make sure to report the attack to your local law enforcement agency and the FBI’s Internet Crime Complaint Center (IC3).
IV. Steps to recover your data
A. Determine the type of ransomware
There are many different types of ransomware, each with their own unique characteristics and decryption methods. Before attempting to recover your data, you’ll need to determine what type of ransomware you’re dealing with.
B. Identify the affected files
Once you’ve identified the type of ransomware, you’ll need to determine which files have been affected. This can help you prioritize which files to recover first.
C. Attempt to decrypt the data
In some cases, there may be decryption tools available that can help you recover your data without paying the ransom.
These tools are often developed by cybersecurity experts and are available for free online.
For More on Data Recovery Please read this article on Data Disaster Recovery
D. Use a professional data recovery service
If you’re unable to recover your data on your own, you may need to enlist the help of a professional data recovery service.
These services specialize in recovering data from damaged or encrypted hard drives and can often recover data that’s been lost due to ransomware attacks.
V. Conclusion
Ransomware attacks can be devastating for businesses, but by following the steps outlined in this guide, you can protect your business from these types of attacks and recover your data if you get hit.
Remember to educate your employees about cybersecurity best practices, keep your software up to date, back up your data regularly, and seek professional help if necessary.